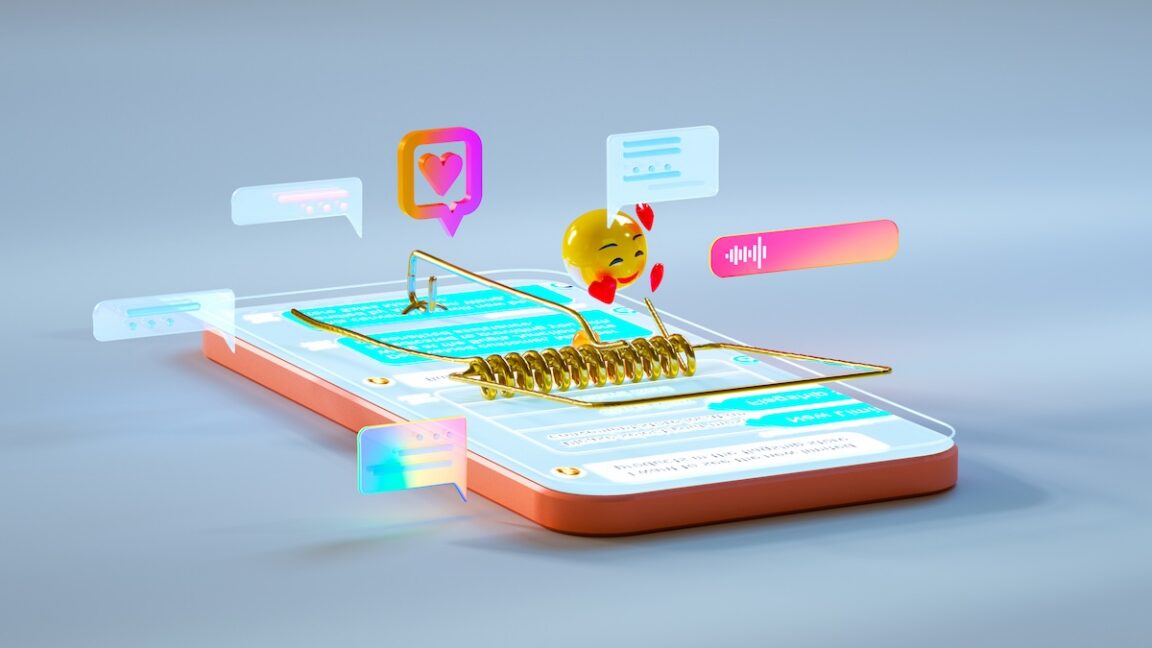
New research shows that authentication flows relying on sign-in links or passcodes sent via SMS can expose sensitive user data across hundreds of services.
The study analyzed more than 700 endpoints on behalf of more than 175 services that deliver such texts, highlighting risks when the tokens in links are enumerated or brute-forced. In some cases, a simple token like 123 can be incremented to access another user’s account, and some links remain valid for years after being sent.
Researchers demonstrated that attackers could view partially completed applications or perform actions in the name of other users, all due to weak authentication tied to tokenized URLs in SMS messages.
While the privacy concerns are clear, many services continue to use this flow because it reduces friction and avoids password management. In contrast, privacy-focused sites have started to embrace email-based magic links, which can be made more secure with short lifetimes and stronger tokens.
Experts recommend that SMS-based sign-in should be replaced or augmented with short-lived, single-use tokens, multi-factor authentication, rate limiting, and secure gateway practices to limit the risk of unauthorized access.














![[AS52888] Universidade Federal de São Carlos (4 probes)](https://r2.isp.tools/images/asn/52888/logo/image_100px.png)
![[AS262393] TIG.com VOCÊ!](https://r2.isp.tools/images/asn/262393/logo/image_100px.png)
